The HIPAA (Health Insurance Portability and Accountability Act) Journal’s August 2025 Healthcare Data Breach Report reflects the sheer frequency of data breaches and violations that continue to plague the healthcare ecosystem. The recurrence of cyberattacks and subsequent patient privacy concerns rings alarm bells. For businesses and organizations functioning in healthcare, such reports make a rather damaging impact on brand image.
Financial penalties are only one side of the coin. Lack of compliance can lead to severe legal consequences, including jail time, and leave a permanent stain on your organization’s reputation. With such high stakes, ensuring the protection of health data and subsequent stringent compliance becomes crucial.
Automation emerges as a remedy for resolving compliance issues and ensuring extended patient well-being. The increased adoption of compliance technology has also illustrated the efficiency of automated workflows in maintaining a patient’s data privacy. Moreover, it ensures timely monitoring of evolving regulations and proves instrumental in removing burdens on legal teams in the sector. As your healthcare organization expands, adherence to global standards of privacy grows more pressing. This guide will assist you in understanding regulatory frameworks, their unique requirements, and the best practices you can undertake for compliance.
Compliance Frameworks: An Overview
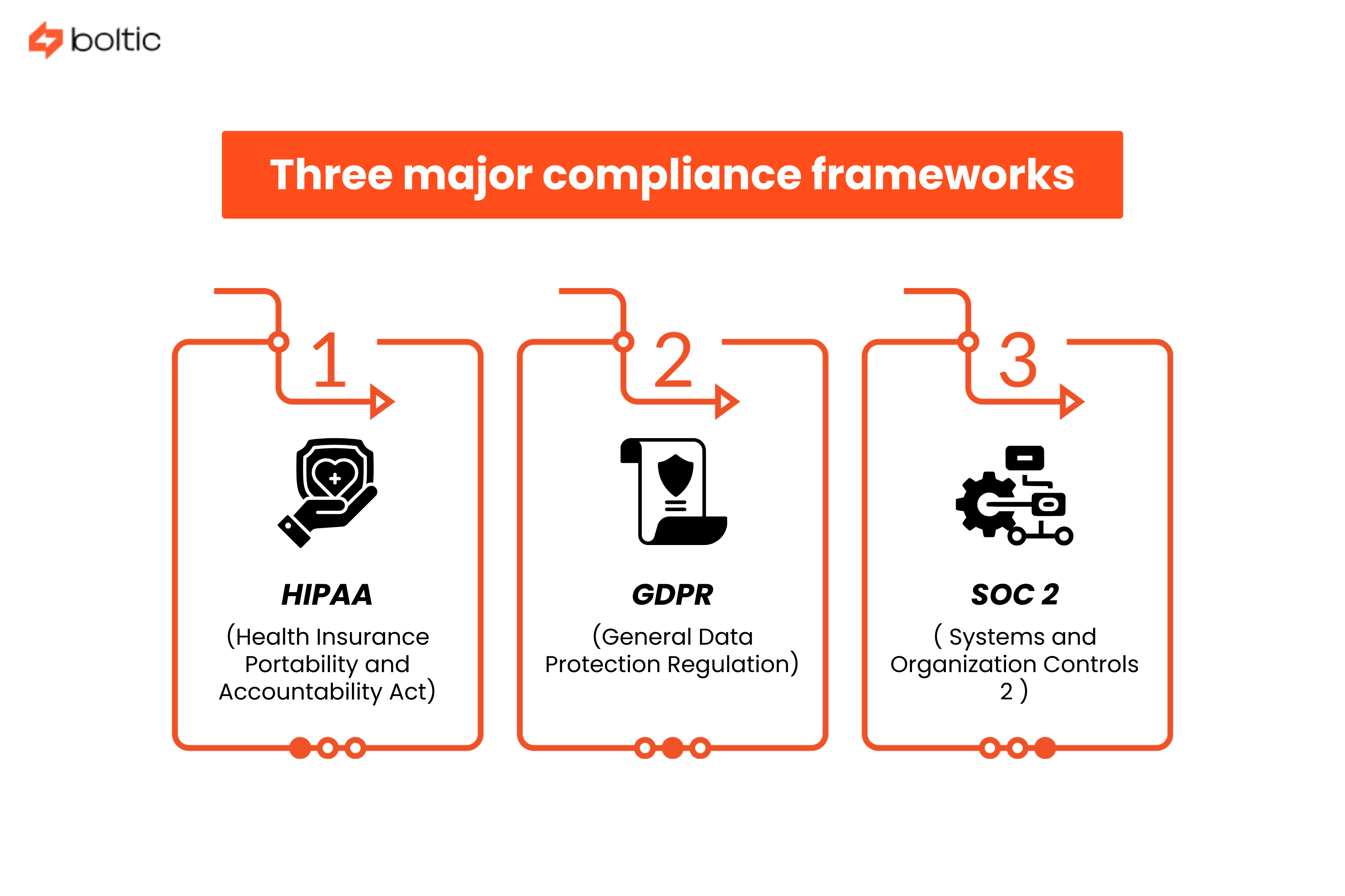
Data protection standards in the healthcare industry can be summed up through three major compliance frameworks:
HIPAA (Health Insurance Portability and Accountability Act)
A foundational law geared toward promoting data security, HIPAA plays a highly consequential role in safeguarding PHI (Protected Health Information) in the US healthcare system. A range of comprehensive administrative and technical defenses come into play, more so in the case of ePHI.
- Security rule, privacy rule, and breach notification rule act as primary pillars for protection
- Outlines strong control policies for the protection of PHI & risk management procedures
- Draws a line between “required” safeguards demanding full implementation & “addressable” safeguards with compliance flexibility
A broad range of healthcare enterprises and service providers fall under its ambit.
GDPR (General Data Protection Regulation)
Responding to the inadequacies of the 1995 Data Protection Directive, European regulators formulated the GDPR to supervise increased private data collection and management by business organizations. With a regulatory jurisdiction that extends to any party, employee, or organization operating within the EU or in relation to it, the GDPR focuses on critical data processing, transparency, and accountability standards.
- Lays emphasis on clear and detailed data mapping of personal information within organizations
- Lays out clear directions for soliciting and sustaining consent for data usage/storage
- Outlines governance and accountability procedures in case of breaches
Impact assessments and frequent employee training for handling sensitive customer data are also mandatory operational requirements under it.
SOC 2 (Systems and Organization Controls 2)
Brought about by the AICPA (American Institute of Certified Public Accountants) in 2010, the SOC 2 framework acts as a checklist for auditors when conducting assessments of an organization’s data security protocols. The five Trust Services Criteria function as the most integral and important component of the security framework.
- Lays out airtight security protocols for data protection
- Outlines security, availability, processing integrity, confidentiality, and privacy as the Trust Services Criteria (TSC)
- Provides for flexibility in data control designs in compliance
SOC 2 audit reports prove beneficial for organizations looking to boost brand reputation and improve scalability.
Analysis of overlaps and differences between all three frameworks:
Here’s a clear analysis highlighting the overlaps and differences between the three key data compliance frameworks:
Data Classification and Inventory: Role In Compliance
Building trust with all stakeholders while ensuring your healthcare business is protected from data breaches and legal consequences begins with data classification. Mandated by global regulatory frameworks, the following measures ensure ethical usage and secure storage of health data.
1. De-Identification of PHI & Personal Data in Workflows
PHI functions as a health-specific dimension of PII (Personally Identifiable Information), while de-identification is a process where data is masked to shield it from breaches. Modifying or altering personal identifiers within your healthcare workflows can ensure de-identification and make data exchanges with third parties secure.
The HIPAA Safe Harbor method provides an 18-point checklist for de-identification and is a requirement under the framework. These 18 identifiers include:
- Names
- Dates
- Full face photos
- Biometric details
- Phone Numbers
- Geographical locations
- Fax numbers (if applicable)
- Social security numbers
- Email addresses
- Medical record numbers
- Bank account numbers
- Health insurance numbers/beneficiary details
- Vehicle identifiers & serial numbers
- Web URLs
- Device identifiers & product serial numbers
- IP addresses and more
These identifiers automatically put health information in the PHI category and are subject to stringent disclosure restrictions.
2. Data Mapping Across Business Systems
Monitoring the data ecosystem of your healthcare organization across multiple business systems makes consistent compliance easier. It flags shadow data and reduces breaches by identifying data existing in unapproved systems.
Data mapping should:
- Include tracking mechanisms for employee, customer, and business data
- Use data models and structures to organize and establish relations between data
- Use an automated process to serve multiple use cases like data migration, integration, transformation, and warehousing
GDPR’s Article 30 highlights data mapping as critical for compliance in organizations that control or process personal data.
3. Maintenance of Compliance Documentation
The collection, maintenance, and storage of reports in a timely, credible fashion ensures compliance while also elevating the reputation of your healthcare enterprise. Careful compliance documentation comes with multiple benefits, such as:
- Proper adherence with regulations and preventing direct & indirect financial loss
- Early spotting of compliance inconsistencies before audits
- Clear communication among internal staff and external stakeholders on corrective data security measures
Proper documentation makes security gaps surface at the right time so risks can be managed and violations can be prevented.
HIPAA: Compliance Essentials
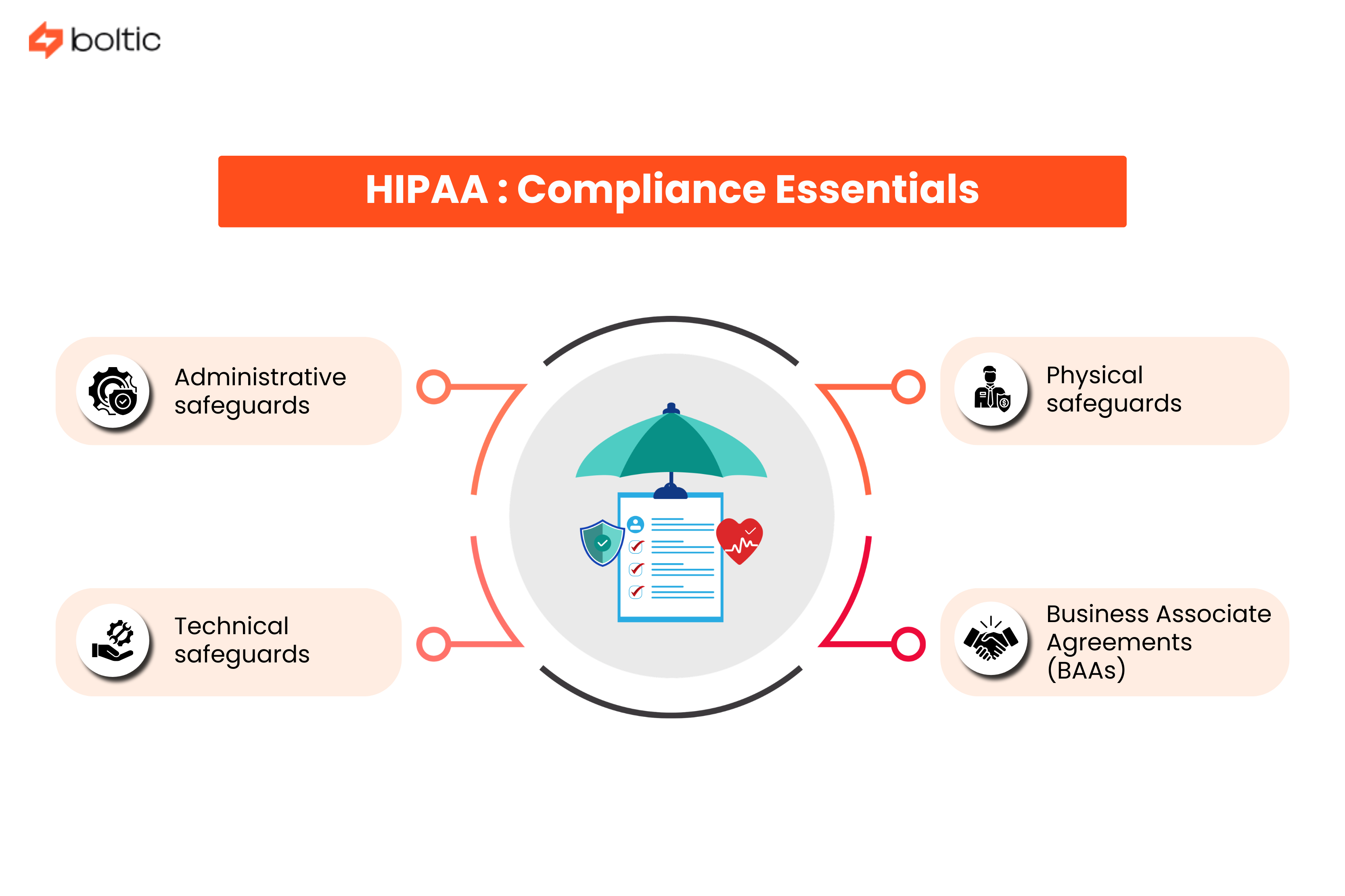
Interrelated regulations in HIPAA determine how healthcare organizations, business associates, and their vendors ought to protect patient information and PHI. Here are the different essentials your organization ought to implement for compliance:
Administrative safeguards:
- Risk analyses and management
- Prompt incident response
- Clear data access policies
- Trained security personnel for safe data handling
Physical safeguards:
- Only authorized access to data centers
- Use of badge systems, biometrics, and restricted keys
- Screen timeouts
- Enforcement of security protocols for select devices to avoid breaches
Technical safeguards:
- Encryption during data exchanges
- Implementation of multi-factor authentication
- Tracking activity across business systems for unapproved usage
- Deploying tools for spotting unauthorized modifications
Business Associate Agreements (BAAs)
- Outline usage flexibility and restrictions by business associate
- Require safeguard implementation from business associates
- Mandatory reporting of unauthorized usage
- Compliance by subcontractors and other third parties
Whether it's a clearinghouse, a service provider, or a health plan, as long as you deal with health information electronically, compliance is indispensable.
GDPR: Data Compliance Requirements in Healthcare
Any organization handling the data of patients and residents within the European Union or engaged with it will have to ensure its data security protocols align with these requirements:
- The organization has a basis rooted in law for accessing and processing health data.
- Data collection is minimal, purposeful, and up to date.
- Children’s/special category data is kept secure through additional security measures
- All data processing activities are documented
- Firm data subject rights are maintained, which enable users to exercise them easily
- Automated decisions can be contested by data subjects
- Timely DPIAs (Data Protection Impact Assessments) are conducted
- Special security personnel are appointed to ensure compliance
- Notifications are promptly issued to supervisory authorities in case of cyberattacks and breaches
- Cross-border data transfers (those beyond the European Economic Area) are governed and monitored
One of the most comprehensive compliance frameworks in the world, the GDPR seeks to ensure protected health data processing.
SOC 2 Type II: Considerations For Privacy of Sensitive Data
Businesses operating in the SaaS and cloud service domains often opt for the SOC 2 Type II framework when managing sensitive customer data. The considerations have been outlined through the five Trust Services Criteria:
- Security - Considered a common criterion, it imposes controls that protect data from use by unauthorized parties.
- Availability - Imposes controls that ensure reliable access during times of use or requirement.
- Processing Integrity - Imposes controls to keep a check on accurate data processing and handling activities.
- Confidentiality - Imposes controls to keep health information and sensitive customer data confidential.
- Privacy - Ensures secure customer data handling while keeping them informed about data retention and disposal.
Furthermore, compliance can be ensured through the use of SOC 2 compliance software and AI agents custom-built for control implementation and audit checks. They can:
- Mitigate risk through single-tenant database architectures
- Remove complex databases and streamline evidence collection
- Continuously monitor, control, and notify of breaches
- Offer extensive scalability for expanding healthcare businesses
- Can aid in managing vendors, agreements, and security certifications
- Can provide audit support and reporting insights
While not a legally enforceable regulation, SOC 2 Type II serves as the gold standard for credibility between businesses.
Best Practices For Ensuring Healthcare Compliance
While efficiency has always been part of the deal, accuracy can now be ensured through streamlined collection, organization, and management of compliance processes. Here are some of the best practices businesses and service providers need to opt for to build and strengthen healthcare compliance:
Encryption and Access Control
Goal: Strengthen data protection for systems that handle PHI to reduce exposure of personal data to risks.
- End-to-end encryption to ensure data securely travels across APIs, databases, emails, and backup systems.
- Management of keys to ensure storage, transfer, and restricted authorization/access.
- Implementation of RBAC (Role-Based Access Control) to control usage authorization based on job role and need.
- Integration of MFA (Multi-Factor Authentication) as an additional layer for verification
Audit Logging and Monitoring
Goal: Ensure uninterrupted visibility across systems and early spotting of inconsistencies to detect violations and report credibly.
- Data access, modifications, deletions, and changes in consent/permission ought to be tracked and logged.
- Logs need to be retained in alignment with regulatory reporting requirements.
- Real-time monitoring configurations need to be set in place for flagging unapproved usage or suspicious activity
- Audit preparations should be streamlined through organized logging and data mapping.
Vendor Due Diligence
Goal: Consider third-party platforms as an extended part of your compliance efforts for removing gaps.
- Run checks and evaluate certifications to ensure third-party platforms are in compliance with regulations.
- Outline clear guidelines for business associates with regard to safeguarding PHI.
- Use shared responsibility models where cloud vendors handle infrastructure, and your HDO (Healthcare Delivery Organization) tackles encryption and access controls.
- Configure through automation to conduct self-scoping questionnaires and compute risk ratings to review vendor security
Incident Response Planning
Goal: Minimize compliance violations through identification, notification, and management of breaches early on.
- Notify supervisory authorities about breaches in compliance with HIPAA, GDPR, and SOC 2 Type II regulations
- Set up automated workflows to detect, contain, and remedy threats in real-time
- Pre-approve templates in workflows for effective internal and external communication during cyberattacks
- Review reports, dashboards, and insights to identify causes and determine corrective actions.
Automation-Specific Considerations
Goal: Integrate automation effectively to improve compliance without increasing risks.
- AI/ML transparency ensures automated decisions can be reported in detail.
- Configure safeguards in alignment with GDPR for maximum compliance.
- Design your workflow to access and collect only the required data to meet legal criteria.
- Include compliance checks in CI/CD (Continuous Integration/Continuous Deployment) pipelines to ensure thorough alignment.
Ethical data protection practices, proper mechanisms for reporting of violations, and automation of critical regulatory procedures can aid organizations in being audit-ready.
Conclusion
Global guidelines and data protection protocols never come to a standstill. They are dynamic and subject to constant changes based on real-time threats and regulatory inadequacies. Healthcare organizations, therefore, cannot afford to run an extensive compliance program one year while dropping the ball in the next.
Compliance is an ongoing process and requires periodic vigilance. Embedding ethical data handling practices into your organization’s operational activities, automating critical processes, and periodically training security personnel creates a compliance-first culture. In the long run, this ensures consistent alignment with existing guidelines and easier compliance with evolving ones.
An AI-powered orchestration and automation platform, Boltic enables your organization to streamline compliance processes through visual workflow builders.
- Build no-code custom workflows for compliance with one or more frameworks
- Integrate business systems securely across the board
- Synchronize data in real-time across all these systems
- Let synthetic monitoring flag inconsistencies and violations
Book a demo and streamline a wide range of healthcare compliance activities in your organization. Leave credibility and reporting to automation while your business teams focus on meaningful security solutions!
drives valuable insights
Organize your big data operations with a free forever plan
An agentic platform revolutionizing workflow management and automation through AI-driven solutions. It enables seamless tool integration, real-time decision-making, and enhanced productivity
Here’s what we do in the meeting:
- Experience Fynd Boltic's features firsthand.
- Learn how to automate your data workflows.
- Get answers to your specific questions.