Compliance in financial services is not a hidden task anymore. It is very important. It directly affects your risk exposure, your operational costs and your customer experience. In 2023 alone, global regulators imposed over $6.6 billion in AML-related fines, according to Fenergo. So you cannot ignore compliance anymore. Using AI in compliance helps you find real problems faster, make new customer accounts quickly and follow the rules properly.
Every day, your teams review identity documents, monitor transactions, investigate alerts and prepare regulatory reports. KYC checks take time. AML alerts pile up. Transaction monitoring systems show thousands of alerts, many of which are false alarms. At the same time, rules keep increasing and regulators are watching more closely.
If you depend too much on manual work, the pressure keeps increasing. That is why automation is now necessary and important for you to use. It makes your checks more consistent, lowers false alerts, speeds up customer onboarding and helps you build trust with regulators.
Let's understand how compliance automation works. Let's see how AI fits into the process, what regulators expect and how you can make a system that balances efficiency with control.
The Compliance Landscape
Banks and financial companies follow many strict rules. Compliance is not just about ticking a legal box. It is an important daily duty that helps you to protect your institution from fraud, heavy fines and other damages.
KYC (Know Your Customer) Requirements
KYC is the basic rule you need to follow in financial laws.
You need to:
- Verify your customer
- Understand why they are opening the account
- Find their risk level
- Monitor their activity over time
AML (Anti-Money Laundering) Regulations
AML regulations require you to detect and report suspicious financial activity. This means your systems can find money laundering, fraud-related financial crimes etc. Strong AML controls are important for you to maintain regulatory trust.
Transaction Monitoring Obligations
Transaction monitoring means checking customer transactions continuously. You must watch for anything unusual. This includes large money transfers or spending patterns that do not match your customer’s normal behaviour.
Regulatory Bodies and Frameworks (FinCEN, FATF, MiFID II)
Several global authorities influence financial compliance standards:
- Financial Crimes Enforcement Network (FinCEN): U.S. AML enforcement
- Financial Action Task Force (FATF): Global AML standards
- European Securities and Markets Authority (ESMA): EU financial market oversight
- Securities and Exchange Commission (SEC): U.S. securities regulation
Penalties for Non-Compliance
Regulators are taking AML and KYC failures very seriously. If you do not follow proper rules, you will have to face heavy penalties.
Here are a few recent examples:
- In 2024, TD Bank in the U.S. paid over $3 billion because it did not monitor suspicious transactions well.
- In India, the Reserve Bank of India regularly fines banks and NBFCs for KYC and AML violations, with hundreds of penalties in 2023 alone.
These penalties usually happen because of:
- Weak transaction monitoring
- Poor customer risk assessment
- Failure to report suspicious activity
- Incomplete documentation
Traditional Compliance Challenges
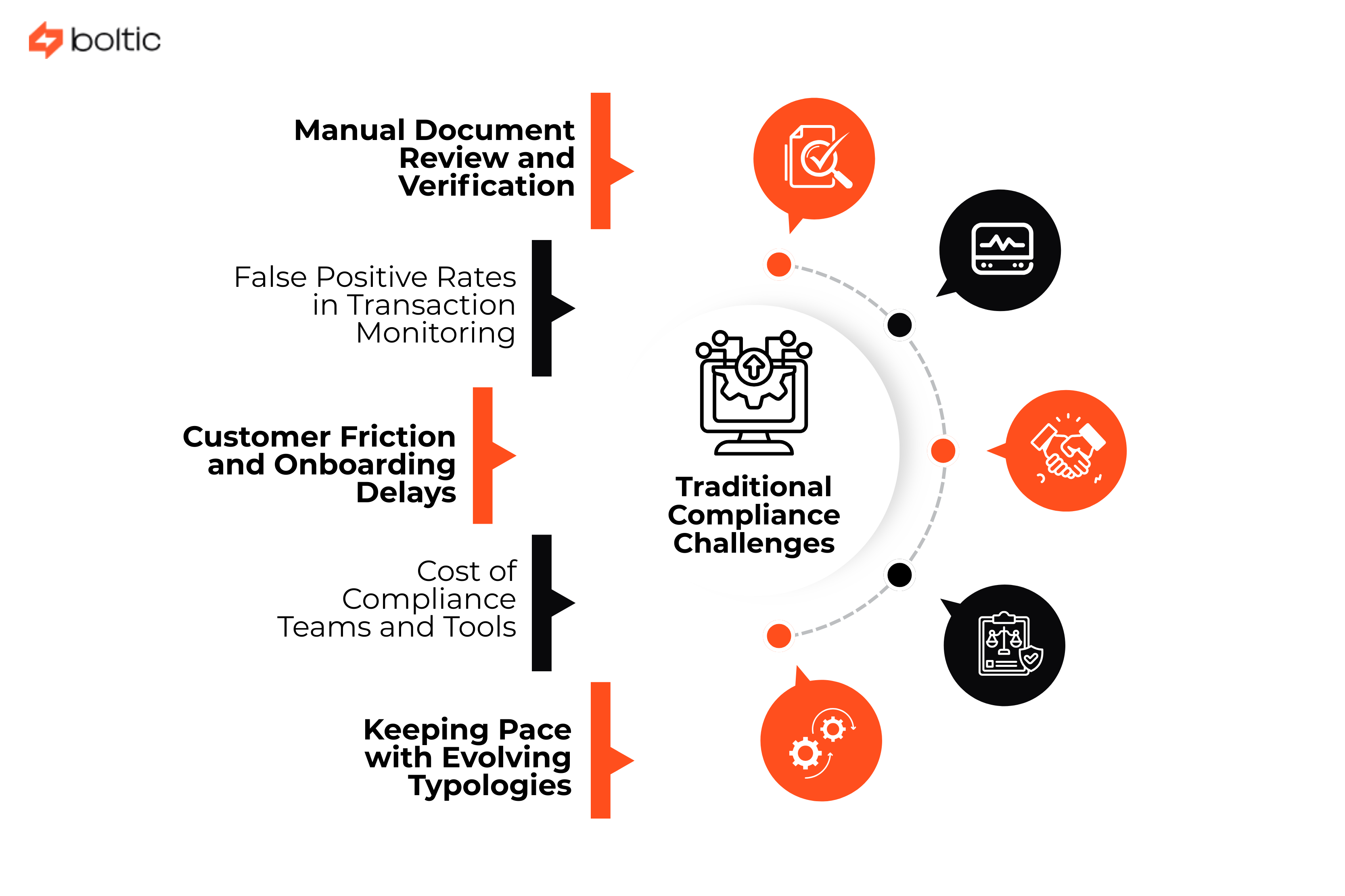
Before automation, most compliance programs relied heavily on manual processes and fixed rules. Here are the most common challenges financial institutions face:
Manual Document Review and Verification
In traditional compliance systems, teams manually review customer documents. This process takes time and can cause risks. When more customers join at the same time, checking everything by hand becomes even more difficult.
False Positive Rates in Transaction Monitoring
Old transaction monitoring systems use fixed rules and limits. Over 90% of alerts can be false positives. This means investigation teams spend most of their time checking alerts that are actually normal transactions.
Customer Friction and Onboarding Delays
Manual KYC processes slow down customer onboarding. When verification needs document resubmission and repeated checks, customers face delays. Some applicants leave the process if it takes too long.
Cost of Compliance Teams and Tools
When rules increase, companies usually hire more compliance staff. They also pay for external screening tools and old monitoring systems. All this costs a lot of money. When companies need even more staff and tools, the total cost keeps increasing.
Keeping Pace with Evolving Typologies
Financial crimes keep changing all the time. Criminals keep changing their tricks to avoid getting caught. This makes it harder for you to find illegal activity.
KYC Automation Architecture
KYC automation removes slow manual work and uses one connected system. Here is how a modern KYC automation framework works:
Document Collection and Verification Workflows
The process begins with digital document collection. Customers upload required documents such as:
- Passport
- Driver’s license
- National ID
- Utility bill
The system checks whether the document is complete and valid before submission.
Identity Verification (IDV) Integration
IDV confirms that the person submitting the documents is real. It prevents:
- Identity theft
- Identity fraud
Data Extraction with OCR and AI
Instead of manually typing customer details, OCR extracts information automatically. AI checks the data and looks for mistakes. This helps avoid manual errors and makes the process faster for you.
Watchlist and Sanctions Screening
Once identity is verified, the system looks at your customer's name in global records to make sure everything is clear.
- If it finds a match, it marks it for review
- If it does not find a match, the process continues automatically
Risk Scoring and Tiering
Every customer is given a risk score. The score is based on factors such as:
- Country of residence
- Type of product or service
- Industry or occupation
- Transaction profile
Customers are grouped into risk tiers such as low, medium or high risk. High-risk customers need extra checks.
Ongoing Monitoring and Periodic Review
KYC continues to monitor customer activity over time. If risk changes, it automatically starts a review. This keeps compliance active and continuous all the time.
Document Processing and Verification
- AI-powered document classification: AI automatically identifies the type of document and sends it to the correct verification workflow.
- OCR for passports, IDs, utility bills: OCR helps to read text from images
- Liveness detection and biometric verification: Proves that a real person is in front of the camera
- Document authenticity checks: Detects fake watermarks, security patterns and inconsistencies in fonts or colors
- Data quality validation and normalization: Checks completeness, format and consistency
Customer Risk Scoring
After verifying a customer’s identity, you need to know how risky that customer might be for financial crime.
Building Risk Models with Relevant Factors
Risk scoring uses a set of factors to decide how risky a customer is. Data is combined to give each customer a risk score. Higher scores get more focus.
Geographic and Product Risk Considerations
Risk is often linked to geography and service types.
For example:
- Customers in high-risk countries may need more checks
- Certain products need higher scrutiny
Regulators encourage you to use geography and products when checking risks.
Politically Exposed Persons (PEP) detection
PEPs are people with important public roles or influence. PEPs have a higher risk because others might use them for money laundering. Automated systems can match customers against global PEP lists to spot them.
Adverse Media Screening
Adverse media means negative news about a person. AI-powered screening checks news and public sources to find risks.
Dynamic Risk Reassessment Triggers
A customer’s risk can change over time. Automatic systems can check risk again when these things happen. This keeps your compliance up to date.
AML Transaction Monitoring
Transaction monitoring looks for signs of suspicious activity in the flow of money. Automated tools use machine learning to find patterns that rules may miss.
Rules-based vs AI/ML Approaches
- Rules-based systems catch things that break set limits
- AI learns from past data and finds odd patterns that rules cannot see
Scenario Design for Suspicious Activity Detection
You need to build different detection scenarios:
- Sudden large transactions
- Fast fund movement
- Transfers to high-risk regions
A good system tests many scenarios and learns which are most important.
Real-time vs Batch Monitoring
- Real-time monitoring looks at transactions while they happen
- Batch monitoring looks at transactions after they are done
For a faster response, you can use real-time.
Threshold Tuning and Optimization
Thresholds need to be correct.
- Too low: Too many alerts
- Too high: Missed suspicious activity
AI helps you to tune thresholds automatically.
Alert Generation and Prioritization
- The system sends warnings when something seems wrong
- Prioritization first checks the most serious warnings
Suspicious Activity Pattern Detection
Automation looks for suspicious patterns beyond single transactions. These include:
- Structuring and smurfing detection: Breaking large amounts into smaller transactions to avoid detection
- Rapid movement of funds: Money moving quickly between accounts
- Unusual transaction patterns for customer profile: Activity that does not match the customer’s normal behavior
- Cross-border and high-risk jurisdiction flows: Transactions to or from countries with high risk
- Trade-based money laundering indicators: Using trade deals to move or hide money
- Cryptocurrency mixing and layering: Sending cryptocurrency in complicated ways to hide where it came from
Alert Investigation Automation
When an alert appears, someone must check it. Automation helps by doing simple steps for you:
- Intelligent case assignment: The system sends alerts to the right person based on workload and expertise
- Automated data aggregation and context: Instead of searching through files, the system collects all related transaction and KYC data automatically
- Transaction graph analysis and visualization: You see linked accounts and flow patterns in simple charts
- AI-assisted investigation recommendations: The system can suggest what to check next based on past cases
- Evidence collection and documentation: All steps are saved in one place for compliance review
Reducing False Positives
False positives are alerts that look suspicious but are actually normal. Too many false positives slow your team down. Automation helps reduce false positives by using smarter analysis, such as:
- Machine learning for pattern recognition
- Behavioral analytics and peer group comparison
- Contextual transaction analysis
- Feedback loops and model refinement
- Measuring and improving precision
Regulatory Reporting Automation
When a case looks suspicious, you may need to file reports with regulators. Automation makes this easier and more accurate for you. Automation helps with:
- SAR (Suspicious Activity Report) generation: These reports are filled faster and with fewer mistakes
- CTR (Currency Transaction Report) filing: These are created when required
- Audit trail and documentation: Everything is documented and stored automatically
- Deadline tracking and workflow management: The system reminds you when a report is due
- Quality assurance and review processes: Make sure no steps were missed before filing
Data Integration Challenges
Automation works best when all systems can share data. You need to connect:
- Core banking systems: So customer accounts and transactions flow automatically
- Payment processor integration: To see all payments in real-time
- Third-party data enrichment sources: It can be sanctions lists or watchlists
- CRM and customer data platforms: It is to use existing customer information
- Data warehouses and analytics: To store and analyze large volumes of data
Explainability and Auditability
Regulators want to understand how your automated systems make decisions. Your automation should give you:
- Model interpretability requirements: The system should show clearly why it gave a customer a risk score
- Decision documentation and trails: Keep a note of all alerts and actions
- Regulatory expectations for AI use: Reports must meet the rules set by authorities
- Human oversight and review protocols: Humans review high-risk cases to make sure accuracy
- Audit preparation and evidence: They are ready for regulator inspections
Privacy and Data Protection
- GDPR compliance in financial workflows: If you work with European customers or data, you need to follow GDPR rules.
- Data minimization principles: Only collect the data you really need. This reduces risk and keeps workflows simpler.
- Customer consent and rights management: Customers have the right to access their own data, can ask for corrections and deletion.
- Secure data handling and retention: Keep data safe at all times to prevent leaks and misuse.
- Cross-border data transfer considerations: International data movement must meet legal standards. Some countries have strict rules for transferring data outside their borders.
Vendor Selection Criteria
Choosing the right automation partner is important.
Implementation Roadmap
- Assessment and gap analysis: See where your current process has weaknesses
- Pilot program design and success metrics: Test automation in a small part of your business
- Phased rollout strategy: Expand automation bit by bit
- Change management and training: Teach your team how to use the tools
- Regulatory notification and approval: Notify regulators where required
This method helps you reduce risk and improve success.
Measuring Success
After automation is live, you should measure results to make sure it is working well. Success measures include:
- Onboarding time reduction
- False positive rate improvement
- Cost per investigation
- Compliance team productivity
- Regulatory feedback and audit results
Good measurement shows real results from automation.
Future Trends
Automation will continue to grow. Some trends include:
- Network analysis and entity resolution: It helps in finding hidden relationships between accounts
- Consortium models and data sharing: Multiple institutions sharing risk data securely
- Quantum computing for pattern detection: There will be faster and more powerful analytics in the future
- Regulatory technology (RegTech) evolution: There will be more specialized tools for compliance
- Central bank digital currencies (CBDCs) monitoring: New systems will need automated checks for digital currencies
Conclusion
Automation in compliance can save you time, reduce errors and make your processes more efficient. At the same time, human judgment is still important to review high-risk cases and make final decisions. Building a culture of compliance is important. When your team understands the rules and follows best practices, your organization stays safe.
Continuous improvement matters. By reviewing alerts, updating rules and learning from past cases, you make your systems smarter as time goes by.
Finally, take advantage of resources and industry associations. Groups like FATF, ACAMS and local regulatory bodies provide you with guidance and networking opportunities to keep your compliance program up to date.
drives valuable insights
Organize your big data operations with a free forever plan
An agentic platform revolutionizing workflow management and automation through AI-driven solutions. It enables seamless tool integration, real-time decision-making, and enhanced productivity
Here’s what we do in the meeting:
- Experience Fynd Boltic's features firsthand.
- Learn how to automate your data workflows.
- Get answers to your specific questions.